The current advancements in automotive technology have paved the way for assistive and autonomous driving systems that heavily rely on radar detection. However, a group of engineers at Duke University, led by Miroslav Pajic and Tingjun Chen, has revealed a system called “MadRadar” that can deceive automotive radar sensors into believing almost anything is possible. This groundbreaking technology is capable of hiding the approach of an existing car, creating a phantom vehicle where none exists, or tricking radar systems into thinking a real car has suddenly deviated from its course. In this article, we will analyze the complexity of MadRadar and its potential implications for radar security.
Modern cars equipped with assistive and autonomous driving systems utilize radar technology to detect moving vehicles in their vicinity. Radar systems also complement visual and laser-based sensors in detecting vehicles both in front of and behind the car. However, due to the multitude of cars using radar on highways, it is unlikely that any two vehicles will have the exact same operating parameters, even if they are of the same make and model. Variations in operating frequencies and measurement intervals make it difficult to develop radar-spoofing systems without prior knowledge of these specific parameters.
Miroslav Pajic’s team at Duke University has successfully created MadRadar, a sophisticated radar-spoofing system that can accurately detect a car’s radar parameters in less than a quarter of a second. Once the parameters are known, MadRadar can send out its own radar signals to deceive the target vehicle’s radar system.
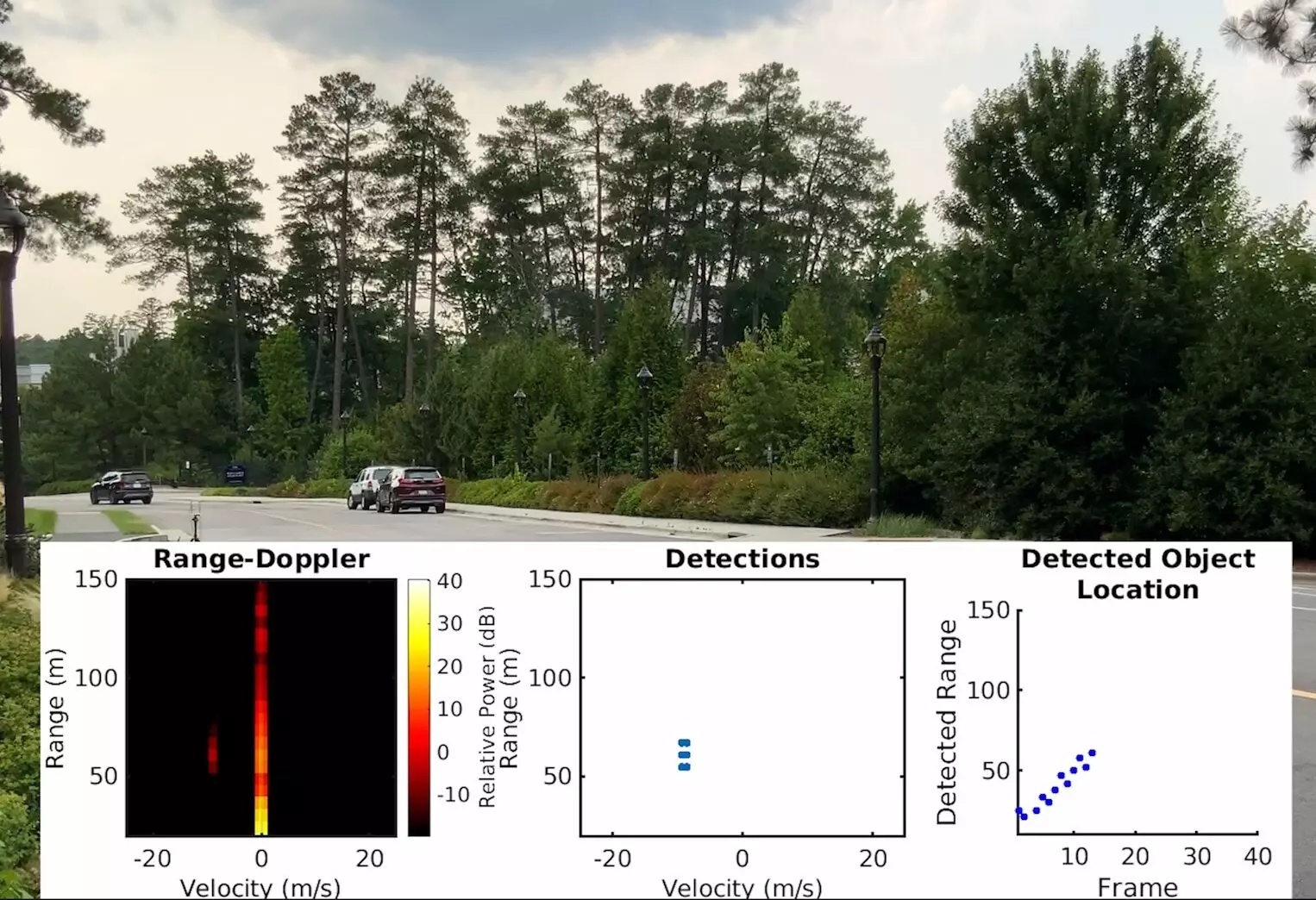
MadRadar showcases its capabilities through three different attack demonstrations. In the first scenario, it creates a phantom car by modifying the characteristics of the radar signal to mimic the appearance of a real contact. This involves manipulating time and velocity to generate a signal that closely resembles a genuine vehicle.
In the second, more complex demonstration, MadRadar fools the target’s radar into perceiving the absence of a passing car when, in fact, one does exist. The system achieves this by carefully adding masking signals around the car’s true location, creating a bright spot that confuses the radar system while maintaining a semblance of normalcy.
The third attack combines elements of the first two demonstrations, making it appear as though an existing car has abruptly changed course. This sophisticated manipulation of the radar signals raises significant concerns about the safety and integrity of radar-based systems.
Miroslav Pajic and his team stress the urgency for car manufacturers to take immediate action in response to the vulnerabilities exposed by MadRadar. They emphasize the importance of fundamentally rethinking the design of radar systems to ensure their resilience against such manipulations.
To mitigate the risks associated with these attacks, the researchers propose randomizing a radar system’s operating parameters over time. Additionally, they suggest implementing safeguards within processing algorithms to identify and block similar spoofing attempts. These precautions are crucial in preventing catastrophic scenarios such as adaptive cruise control malfunctioning, leading to dangerous driving situations.
While MadRadar’s demonstrations primarily focused on automotive radar systems, the broader implications of these findings should not be overlooked. Radar technology is not limited to cars, and these vulnerabilities could potentially affect other radar-based systems in various sectors.
Miroslav Pajic highlights that the lessons learned from MadRadar extend far beyond automotive applications. The need for better radar security and countermeasures applies to industries relying on radar systems for critical operations. As technology continues to evolve, it is imperative to invest in robust solutions to protect against potential threats.
MadRadar represents a groundbreaking research development in the field of radar security. The system’s ability to manipulate radar signals with minimal prior knowledge poses a significant challenge to the integrity of current radar-based systems. As the automotive industry continues to embrace radar-driven technologies, it is essential for manufacturers to reevaluate their system designs and implement stringent security measures to mitigate the risks associated with these vulnerabilities. Furthermore, the lessons learned from MadRadar should serve as a wake-up call for industries beyond automotive to enhance their radar security and protect against potential threats.

Leave a Reply